1. What application layer protocol is commonly used to support for file transfers between a client and a server?
HTML
HTTP
** FTP
Telnet
2. What are two forms of application layer software? (Choose two.)
** applications
dialogs
requests
** services
syntax
3. A network administrator is designing a network for a new branch office of twenty-five users. What are the advantages of using a client-server model? (Choose two.)
** centralized administration
does not require specialized software
** security is easier to enforce
lower cost implementation
provides a single point of failure
4. What is the purpose of resource records in DNS?
temporarily holds resolved entries
** used by the server to resolve names
sent by the client to during a query
passes authentication information between the server and client
5. What is the automated service that matches resource names with the required IP address?
HTTP
SSH
FQDN
** DNS
Telnet
SMTP
6. What three protocols operate at the Application layer of the OSI model? (Choose three.)
ARP
** DNS
PPP
** SMTP
** POP
ICMP
7. What are three properties of peer-to-peer applications? (Choose three.)
** acts as both a client and server within the same communication.
requires centralized account administration.
** hybrid mode includes a centralized directory of files.
** can be used in client-server networks.
requires a direct physical connection between devices.
centralized authentication is required.
8. Which application layer protocols correctly match a corresponding function? (Choose two.)
DNS dynamically allocates IP addresses to hosts
** HTTP transfers data from a web server to a client
POP delivers email from the client to the server email server
SMTP supports file sharing
** Telnet provides a virtual connection for remote access
9. Which email components are used to forward mail between servers? (Choose two.)
MDA
IMAP
** MTA
POP
** SMTP
MUA
10. As compared to SSH, what is the primary disadvantage of telnet?
not widely available
** does not support encryption
consumes more network bandwidth
does not support authentication
11. Which statements are correct concerning the role of the MTA in handling email? (Choose three.)
routes email to the MDA on other servers
** receives email from the client's MUA
receives email via the POP3 protocol
** passes email to the MDA for final delivery
** uses SMTP to route email between servers
delivers email to clients via the POP3 protocol
12. Which two protocols are used to control the transfer of web resources from a web server to a client browser? (Choose two.)
ASP
FTP
HTML
** HTTP
** HTTPS
IP
13. A small home network has been installed to interconnect three computers together for gaming and file sharing. What two properties represent this network type? (Choose two.)
User accounts are centralized.
** Security is difficult to enforce.
Specialized operating system software is required.
File permissions are controlled by a single computer.
** A computer that responds to a file sharing request is functioning as a server.
14. Which layer of the OSI model supplies services that allow user to interface with the network?
physical
session
network
presentation
** application
transport
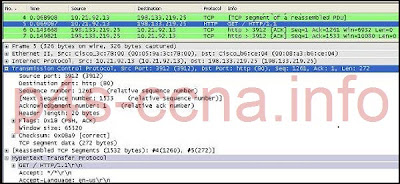
15.
Refer to the exhibit. What is the destination port for the communication that is represented on line 5?
** 80
1261
15533
3912
65520
16. What are two characteristics of peer-to-peer networks? (Choose two.)
scalable
one way data flow
** decentralized resources
centralized user accounts
** resource sharing without a dedicated server
17. What application layer protocol describes the services that are used for file sharing in Microsoft networks?
DHCP
DNS
** SMB
SMTP
Telnet
18. What are two characteristics of clients in data networks? (Choose two.)
use daemons
** initiate data exchanges
are repositories of data
** may upload data to servers
listen for requests from servers
19. What is the role of the OSI application layer?
provides segmentation of data
provides encryption and conversion of data
** provides the interface between the applications on either end of the network
provides control of all the data flowing between the source and destination devices
20. How does the application layer on a server usually process multiple client request for services?
ceases all connections to the service
denies multiple connections to a single daemon
suspends the current connection to allow the new connection
** uses support from lower layer functions to distinguish between connections to the service
Subscribe to:
Post Comments (Atom)
Popular Posts
-
Hot nude scenes of Kim Min Sun ....! Large | Medium | Small | By webmaster ] Trailer of the film "Portrait of a Beauty" wa...
-
click here to view full size
-
Rolls-Royce says one part caused Qantas A380 blow-out Rolls Royce engine The engine broke apart on a Qantas A380 aircraft on 4 November Cont...
-
Top 25 body 'sexy' best bikini Tuesday, 08/06/2010 16:00 (2Sao) - Home entertainment network information can count the number of...
-
Cisco has very recently launched the new version of Packet Tracer 5.1. I have uploaded the software with tutorials for the users who are pr...
-
Angelina Jolie had to do incest with her stepfather at age 16 Large | Medium | Small | By webmaster ] After a drunken night with t...
-
1. Which two things can be determined by using the ping command? (Choose two.) the number of routers between the source and destination dev...
-
Renault can name new car Zoe as girls' case rejected Renault's zero-emissions car, Zoe, due for release in 2012 Renault has been giv...
-
1. Refer to the exhibit. Host B attempts to establish a TCP/IP session with host C. During this attempt, a frame was captured at the FastEth...
-
Go bar dancing hobby's drunk teen girl from china Author: l_lovestory_l 01:22 - When night falls cover the city of Beijing is also...



3 comments
Thanks
thank you verry much
What I will discuss further with you,
Post a Comment